Four Pillars
Our mission...simple; making your investments in technology and support, assets to the organisation. At ABSS Inc, we are able to leverage our technological ingenuity and skillsets while also tempering our work with the professional courtesy required for meeting client neccessities efficiently and concisely.
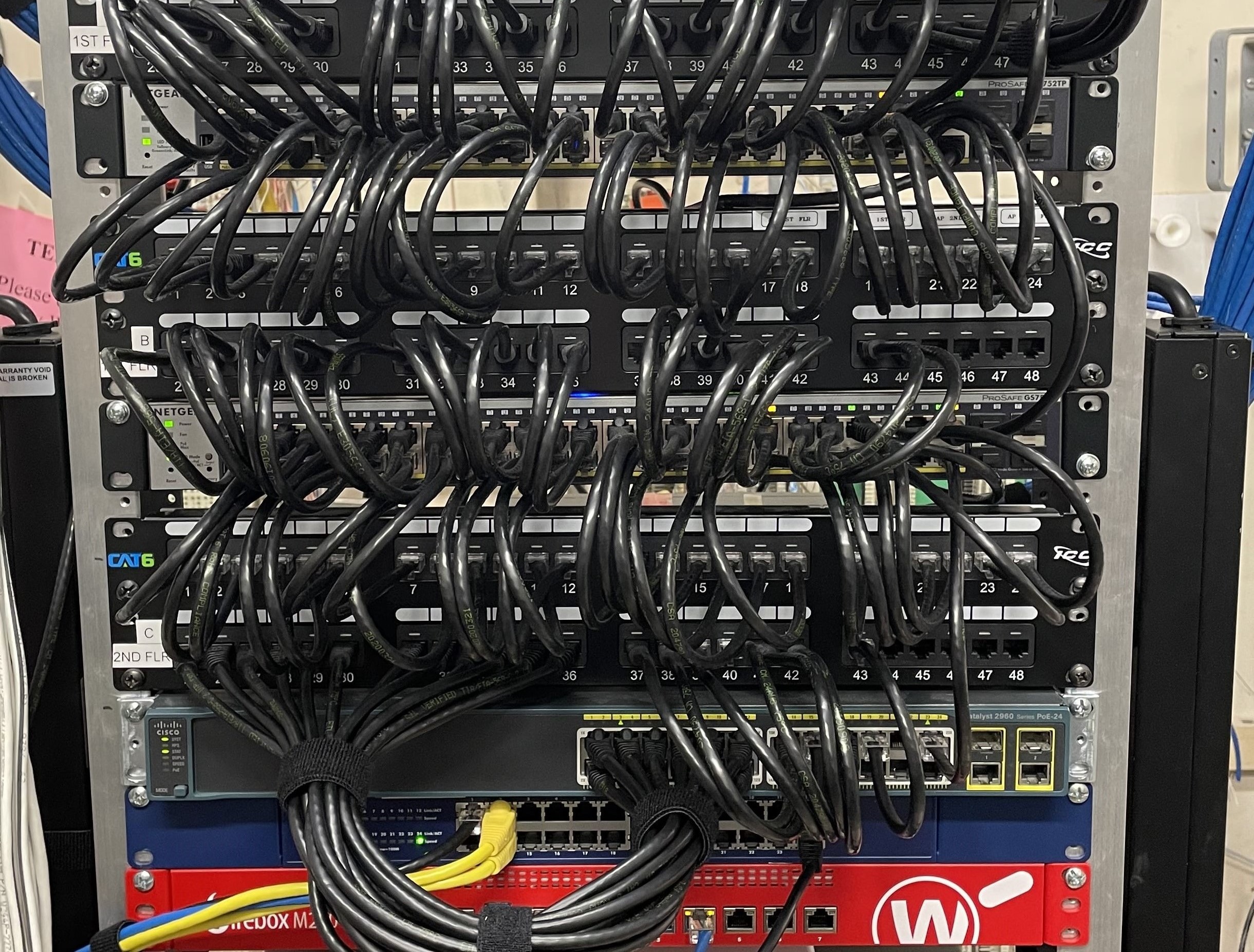
Networking
We provide insights necessary for maintaining network health, helping prevent/address issues and contribute to the overall reliablility of the IT infrastructure
World-Class IT Services
Representing a comprehensive approach to tech that inhibits growth, efficiency, and innovation while adhering to the highest standards of quality and customer satisfaction - we go beyond the basic technical support.
Recovery
Our network recover strategies contribute to the overall business continuity, data protection and stability of network operations. Gone are those days where you experience the extremities of downtime. Our tailored solutions provide the platform for operations throughout most manageable disasters.
Security
Today's interconnected and digital world holds network security as paramount. We help mitigate the increasingly sophisticated cyber threats that underscore the importance of implementing comprehensive security measures.
Happy Clients
Projects
Hours Of Support
Hard Workers





Services
Our packages are comprised of various services that can also be serperated for a more focused approach to organizational needs.
Managed IT Solution
Helping improve efficiency, reduce operation costs, enchance security, and access specialised IT skills that align with the organizations' requirements and goals.
Network & Security Auditing
Organizations can proactively demonstrate their commitment to protecting sensitive data and assets with regular audits
Network Design
From small business to enterprise...we'll create a network that works for your organization with growth projections taken into consideration
Remote Monitoring Management
Transforming the ways organizations operate by providing real-time insights, improving efficiency, and enabling proactive decision-making
Data Recovery & Continuity
Ensuring organizations can effectively manage unexpected disruptions and maintain access to critical data and services
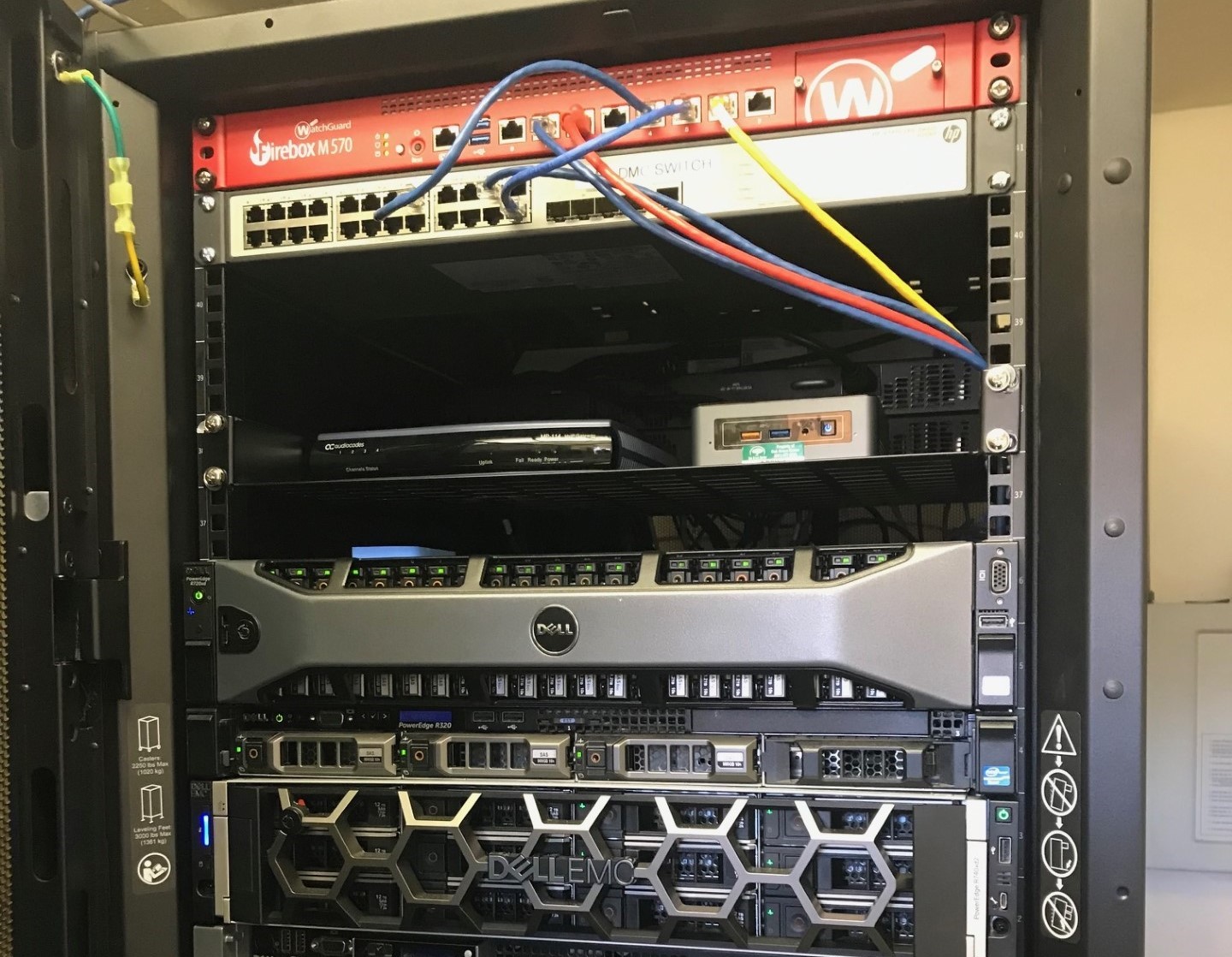
Datacenter Hosting & Co-Location
Each choice depends on your organizational needs, resources and/or preferences. Clients may require full control, have a need to be most secure and cost-effective, or need a hybrid approach.
Why Us
ABSS Inc. has provided the highest level of professional support to our clientele reaching all over the Northern and Southern regions of California. For over 30 years, we've maintained a multi-faceted approach to IT services, products and solutions having proven beneficial for both client and service provider alike. So...why ABSS Inc?
AICPA SOC-2 Certified
Evaluation of controls related to security, availablity, integrity, confidentiality and privacy.
NCUA & FFIEC Competent
Compentencies with both associations when undergoing examinations and audits
Tailored Solutions
We are more than aware that there is not a 'one size fits all'. Regardless, we are here for you
Portfolio
We believe in the importance of documenting projects and keeping our portfolio as up to date as possible. With growth, we will undertake more projects, achieve new milestones and will regularly update you. This tells the story of our growth, expertise, and our commitment to delivering exceptional results.
- All
- 2023
- 2022
- 2021 & Before
Packages
We understand that there is no solution that fits every business the same. Picking a package is only the beginning...a 'pick and mix' approach is often how we manage and protect every digital corner of the organisation.
Sole Service
- Remote Monitoring Management
- External Vulnerability
- Office 365 Management
- Disaster Recovery
- Consultations
Server in a Box (SiaB)
- Managed Hosted Virtual Network Server
- Shared storage environment
- Microsoft software assurance
- Secured off-site backups
- 24*7*365 remote access
Total Care

- Security Monitoring & Reporting
- Patch Management & Remediation
- Reduced on-site rates
- Email Filtering
- Tailored solutions
Frequently Asked Questions
Here are just some example FAQ's that reflect the unique aspects of ABSS' products, services, and client enquieries
-
What industries do ABSS Inc. serve?
Our clientele profile is comprised of many different industries from education sectors to terraforming construction companies. Any company with digital assets to secure and protect is where you'd find ABSS Inc.
-
What products does ABSS Inc. offer?
ABSS Inc. provides various products such as email filtering, endpoint detection & response, remote monitoring management and more to added in the upcoming year.
-
Are the services offered by ABSS Inc. customisable?
Yes ABSS Inc. takes pride in organisational fitment of our packaged solutions, giving you the best fitment for the best price.
-
How do you ensure privacy and security of our data and workstations?
We implement industry best practices, including encryption, regular security audits, and strict access controls to safeguard your data and hardware.
-
Is our data stored on your server?
Yes, we provide cloud-based solutions, which means your data is stored on our secure servers. We prioritize data privacy and compliance.
Contact
ABSS Networks is proud to bring decades of experience, spanning across unrelated industries, to facilitate each and every client request we encounter. If you have any questions regarding network security, network design, disaster recovery, network auditing, hosting, and/or world-class IT services; we are here to help. Please feel free to call us during regular business hours. You can also reach us via contact form, 24/7. No matter how you decide to get in touch with us, we look forward to hearing from you soon.